Love your live streaming gear? But what if your IT guy doesn’t want it on the network? Avoid a network security “gotcha” and ask the right questions about the security of your live streaming gear before buying.
So you did your homework and got the best live streaming gear for your budget and application. Now you want to connect it to your company’s enterprise network and start streaming video content, but the IT guy stops you dead in your tracks. Before choosing any new live streaming gear, it’s important to know the network access and security requirements of your network to avoid any nasty “gotchas” after the fact.
Enterprise networks are controlled environments and it’s the IT administrator’s job to identify network security vulnerabilities and eliminate threats. Every device on the network and all confidential data needs protection from threats like man-in-the-middle attacks, unauthorized access, viruses and malware. AV equipment is no longer just AV, they’re streaming servers with IT functions that need to be treated as IT gear. If the gear you want to connect doesn’t comply with the network’s security policies, don’t blame your IT guy if he sees that as a threat.
Some common network security measures that are put in place include:
- network security protocols like 802.1x
- authentication certificates and passwords for access control
- data encryption
- firewalls
Asking your IT guy to add a device to the network that does not comply with network security policies means asking him to break his own security policies and do things like open ports on the server. On the other hand, IT friendly gear can identify itself as a trusted device on the network and is a lot easier to deploy. Encoders that comply with network security requirements are safer and support features like presenting a valid security certificate or password for network access. Simply contact the IT guy and ask for the network access protocol they’ve deployed and the current security certificate or password to get your gear on the network.
AV equipment is no longer just AV, they’re streaming servers with IT functions that need to be treated as IT gear
Another concern is how to go about protecting confidential content that’s streaming over the network. Whether it’s corporate-wide meetings, employee information sessions, or internal training, the streaming encoder should encrypt the content before it is streamed over the network. Secure AV gear uses Real Time Messaging Protocol Secure (RTMPS) to encrypt the live stream and SFTP for secure file transfers, which should satisfy the data protection requirements without requiring additional effort from IT.
Things get even more difficult when you need to connect your gear on someone else’s network. Many venues like schools, government departments, private businesses and hospitals have private local area networks (LANs) with their own set of network security policies. If you think convincing your own IT administrator to connect insecure AV equipment to the network is a challenge, how challenging do you think it is to ask an IT administrator at some remote, off-site location to open up his network ports and connect your live streaming gear when it has no built-in security features?

When setting up for a live streaming event at an off-site location, arranging to meet with the IT administrator before you step foot on location can save you a lot of frustration. The last thing you want happening is showing up ready to test your live stream only to discover there’s no Internet access and the IT administrator is nowhere to be found.
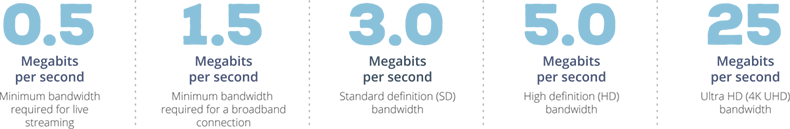
But don’t most places offer a public network for guests to connect to the Internet without needing access to the private network? Why not just use that for live streaming and avoid the whole security and network access issue? The problem is that most public networks don’t have enough bandwidth and you can’t be sure how many people will log on during your live stream. You need dedicated bandwidth for live streaming, so plan to use the private network.
You’ll want to make sure that your encoder supports security features and currently, very few of them do – so choose carefully.
Wrap it up!
Remember that an IT administrator’s job is to make sure that the device you’re connecting to the network and the content you’re streaming won’t pose a security threat. Choosing an IT friendly live streaming encoder like the Epiphan Pearl-2 and Pearl Mini with built-in network security makes connecting to enterprise networks easier, takes less time and effort to deploy, and won’t compromise network security. Look for AV gear with security features like 802.1x certificate authentication, PEAP user name and password support, RTMPS encryption for live streams, SFTP and HTTPS support for encrypted admin access.
